
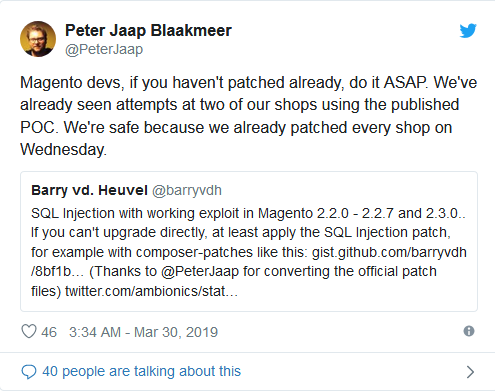
A recently patched SQL injection flaw affecting the popular open-source e-commerce platform Magento is being actively exploited by attackers, so if you haven’t implemented the provided security update or patch, now is the time to do it.
It’s an SQL injection flaw which can be exploited with no authentication or privileges, which is why for admins tending sites using Magento it’s a stop what you’re doing and patch this now situation.
The affected versions are:
- Version 1 before 2.1.17
- Version 2.2 before 2.8,
- Version 2.3 before 3.1
- Magento Open Source before 9.4.1
- Magento Commerce before 14.4.1
To protect against this vulnerability and others, you must upgrade to Magento Commerce or Open Source 2.3.1 or 2.2.8. We strongly suggest that you install these full patches as soon as you can. And if you can’t do that contact the Expert Magento Web Developer.
Source: https://www.helpnetsecurity.com/


